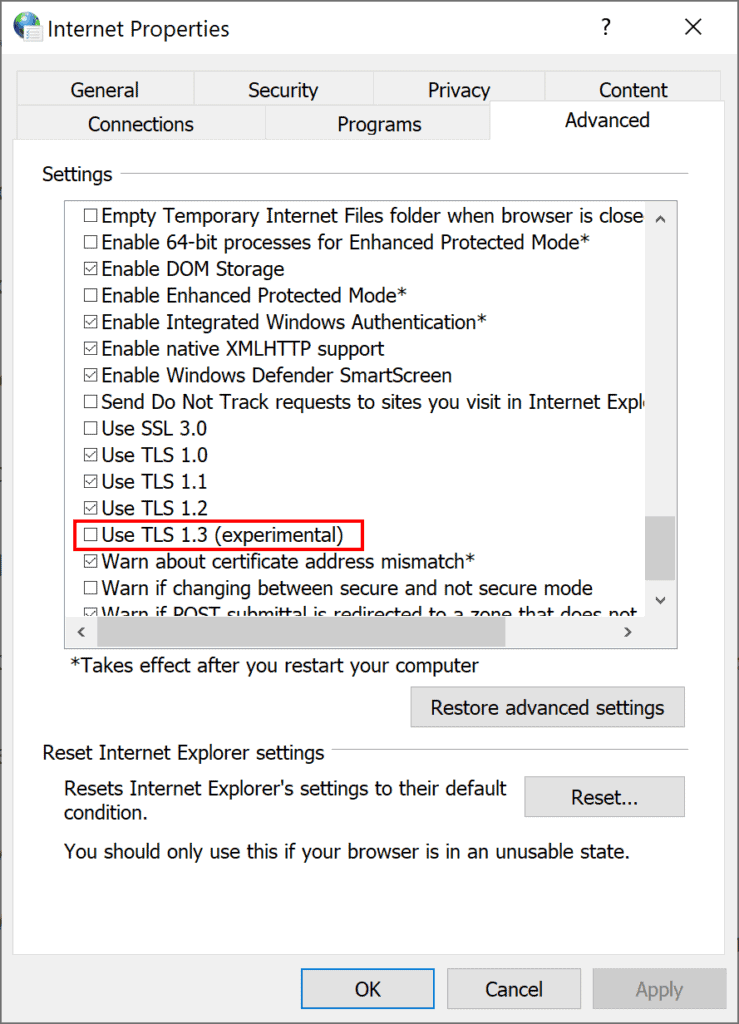
Microsoft announced this week that it enabled TLS 1.3, the latest version of the security protocol, in the latest Windows 10 builds starting with build 20170. The company notes that TLS 1.3 is enabled by default in IIS/HTTP.SYS, and that Microsoft Edge Legacy and Internet Explorer administrators may enable it in the Internet Options under Advanced.
The new Chromium-based Microsoft Edge browser supports TLS 1.3 out of the box according to Microsoft. It does not use the Windows TLS stack
Support for TLS 1.3 will also be added to .NET versions 5.0 and newer.
The enabling of TLS 1.3 in recent Windows 10 builds is the first step in the wider adoption of the security protocol on Windows 10. The company has not revealed when it plans to enable it in stable versions of Windows 10. It seems unlikely that TLS 1.3 will be enabled in the next feature update for Windows 10, Windows 10 version 20H2. A more likely candidate is Windows 10 version 21H1, the first feature update of the coming year; this would also coincide with the disabling of TLS 1.0 and 1.1 which Microsoft announced won’t happen before Spring 2021.
The company announced plans to deprecate the older weaker security protocols TLS 1.0 and 1.1 in its Windows operating system in the first half of 2020. Other companies, Google, Mozilla and Apple in particular, also announced that they would remove support from their browsers. TLs 1.3 can be enabled in Chrome and Firefox already.
The global pandemic of 2020 delayed the removal of the older protocols and Microsoft noted in August 2020 that both protocols won’t be disabled until Spring of 2021 at the earliest.
Update as of 8/14/2020: The plan to disable TLS 1.0/1.1 by default is being updated for Internet Explorer and Microsoft Edge Legacy. TLS 1.0 and TLS 1.1 will not be disabled by default for either browser until Spring of 2021 at the earliest. Organizations that wish to disable TLS 1.0 and TLS 1.1 before that time may do so using Group Policy.
TLs 1.3 promises better security and performance over older protocols. Microsoft recommends that developers start to test TLS 1.3 in their applications and services as soon as possible. The Windows 10 stack will support three cipher suites to reduce complexity and to guarantee “certain security properties”.
The supported cipher suites are:
- TLS_AES_128_GCM_SHA256
- TLS_AES_256_GCM_SHA384
- TLS_CHACHA20_POLY1305_SHA256
The third cipher suite is not enabled by default.
The protocol enables encryption earlier in the handshake, providing better confidentiality and preventing interference from poorly designed middle boxes. TLS 1.3 encrypts the client certificate, so client identity remains private and renegotiation is not required for secure client authentication.
Author Profile
Latest entries
 Tips & TricksNovember 7, 2025master_not_discovered_exception in Palo Alto Networks Log Collector
Tips & TricksNovember 7, 2025master_not_discovered_exception in Palo Alto Networks Log Collector Tech NewsAugust 17, 2025Malware Analysis For Remcos Remote Access Trojan (RAT)
Tech NewsAugust 17, 2025Malware Analysis For Remcos Remote Access Trojan (RAT) Tech NewsJune 10, 2025How to register and install iOS 26, iPadOS 26, and macOS Tahoe
Tech NewsJune 10, 2025How to register and install iOS 26, iPadOS 26, and macOS Tahoe Tech NewsJune 1, 2025How to Install Cisco and Juniper Images in EVE-NG
Tech NewsJune 1, 2025How to Install Cisco and Juniper Images in EVE-NG
0 Comments